Long-term care cyber-attacks are on the rise. From single-location facilities to nationwide organizations, the long-term care industry is facing cyber threats like never before.
How can you keep your long-term care organization safe from attacks? The first step is to know what you’re dealing with.
Threat Type #1: Email Phishing Attacks
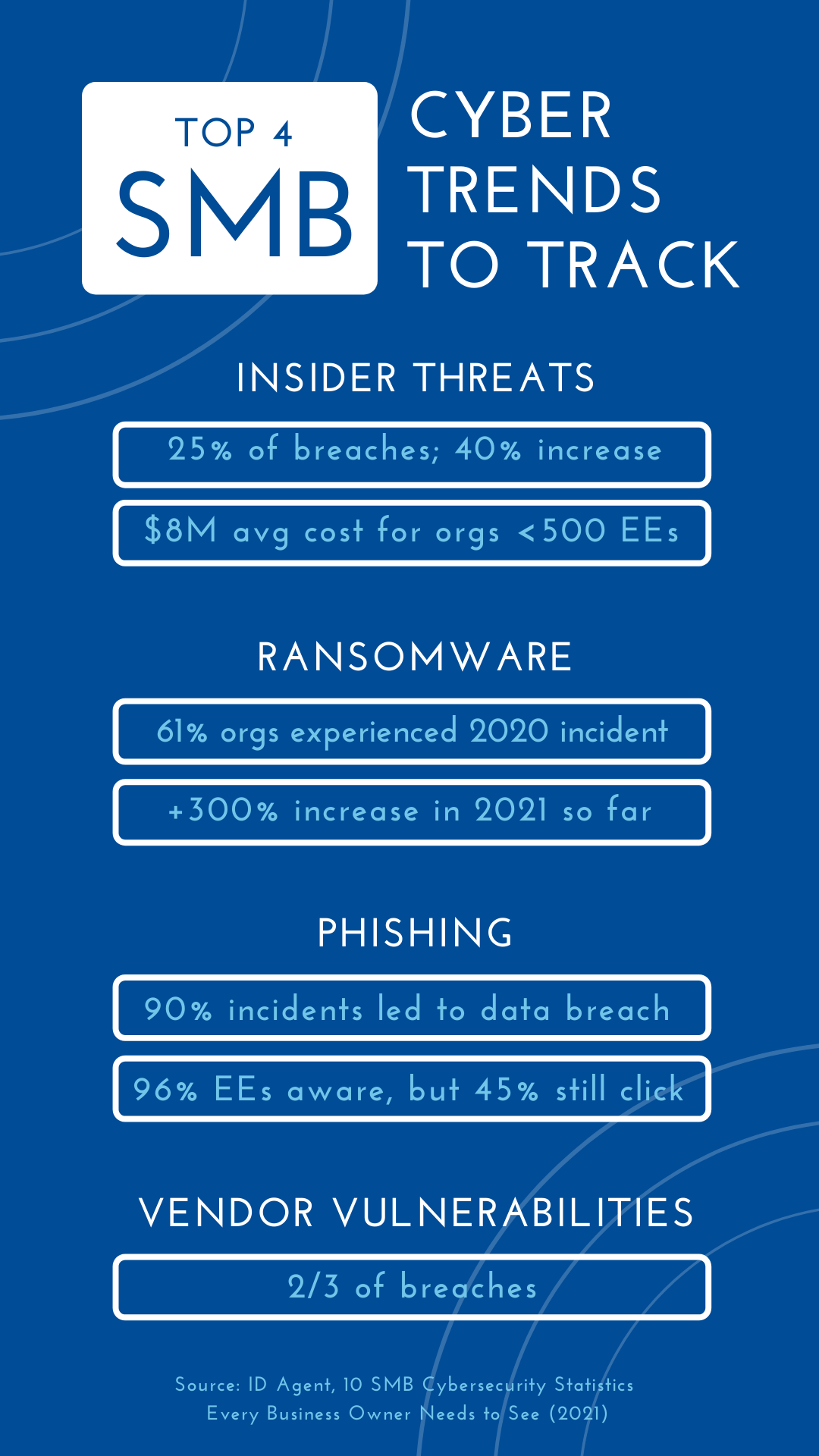
By far the most common cyber-attack, email phishing is when a hacker attempts to gain protected information (usually passwords) through deceptive means. Often, victims will receive an email from a trustworthy individual or organization insisting that they click a link or fill out a form. As soon as they do, the hacker captures their information and can use it however they wish.
Phishing attacks are dangerous because they rely on human error, not software loopholes or vulnerabilities. The emails often seem credible. For instance, your staff might receive a bulk email from you stating that their passwords have been reset and that they must enter their login information to confirm. They click the link in the email, which takes them to a landing page that looks exactly like software your organization uses. Since it looks legit, they enter their information, and the attackers now have access to your systems.
Staff training and vigilance can reduce the likelihood of a successful phishing attack, but it only takes one slip-up to compromise your security.
Threat Type #2: Ransomware / Malware Attacks
Malware attacks are viruses, worms, Trojan horses, spyware, or any other type of malicious software application that a user downloads to your system. The programs themselves can do anything imaginable to your network. Some malware simply hides or deletes information. Other programs shut out users or make certain applications totally inoperable.
A malware attack becomes a ransomware attack when the hackers offer to reverse the damage they have caused for a monetary payment. Larger organizations have paid ransoms in the millions of dollars just to get their systems back online.
Malware and ransomware attacks are initiated through clicked links or file downloads. Once downloaded, the program attaches itself to different files and gets to work. Email filters and other scanning programs help, but hackers are finding more and more ways to get these files onto your organization’s computers.
Threat Type #3: Social Engineering Attacks
Phishing isn’t the only cyber-attack that relies on human error. Other types of cyber-attacks take a different, yet still personal, approach to stealing information.
Baiting is a type of cyber-attack that promises a desirable good in exchange for a user’s information. For example, a website might offer free music downloads for providing your email login and password.
Pretexting is all about the story. The attacker creates a plausible pretext for requiring the information they ask from you. For instance, they might ask for your full name, social security number, and mother’s maiden name to confirm your identity. In reality, they’re using that information to commit identity theft.
In the end, your best defense against cyber-attacks is education. Talk to your staff about cyber-attacks and make sure they understand what’s really at stake.
Beyond your employees, consider partnering with an IT provider to secure your long-term care organization’s data against cyber-attacks. For instance, Prime Care Technologies offers a highly secure Tier III+ data center as well as a separate disaster recovery center to its clients.
It’s not a question of if you’ll be the victim of a cyber-attack — it’s when. And when it happens, don’t you want to be ready?
/Prime-Care-Technologies-Logo.png?width=191&height=55&name=Prime-Care-Technologies-Logo.png)


