It’s that time of year again.
It’s that time of year again.
In 2011, the desolation and loss of life in the wake of the massive tornados in Joplin, MO, in Tuscaloosa, AL, and other states have captured the attention of LTC providers across the country with the realization that disasters can strike anywhere, at anytime. They recognize the need for a real-world, workable, and well-rehearsed disaster preparedness and recovery plan that at least minimizes, if not prevents, injury and loss of life during and after a disaster.
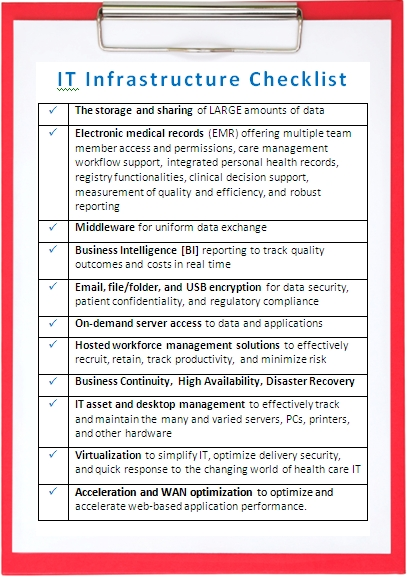
Post-disaster recovery, however, must also encompass access to resident information, because in the world of EMR, electronic data can be lost if the servers or other storage devices are damaged by fire, flooding, or building collapse. Fortunately, there are steps which you can implement now to protect that vital information before a disaster strikes.
Backup procedures (a good start) - A basic IT disaster preparedness plan must include a regularly-scheduled daily back-up of data with off-site storage and I don’t mean in an employee's home. Tip: One important thing to remember about backups: they should be regularly tested. Nothing is more frustrating than to need a backup and find that the data is corrupt or non-existent.
Fault tolerance - The next step up in disaster recovery is to build fault tolerance into all of your critical systems. This means installing Redundant Array of Independent (or Inexpensive) Disks (RAID) drives (disk drives which are redundant copies of each other), clustered systems, and other types of local recovery procedures.
What happens if - Once you have a good backup and archiving procedure with critical fault-tolerant systems in place, the next step is to put together procedures for remote disaster recovery.
Option: Co-location
You might, for example, make arrangements with another company to share equipment and space if either is struck by disaster. Such an arrangement also requires agreements with critical computer vendors to quickly ship new systems in the event of an emergency. Although recovery would be slow, this kind of planning is a good first step.
Option: A Split Site
Some companies are large enough that the IT department could be staffed at more than one location. In the event of a disaster to one site, operations would simply shift to the other.
Option: A Cold Site
This is a site (often managed by a third party and shared among multiple clients) which is stocked with equipment and ready to go. The remote servers are generally not “live,” and time is required to activate the off-site system should the need arise. This is a popular disaster recovery method, because it tends to be less expensive than other options and gives a company the ability to be up and running with a brief delay.
Option: A Warm Site
If a company has the resources, then a warm site is a viable alternative. This is a site which is pre-positioned with equipment, software, and other necessities ready to go in the event of an emergency. The equipment is idle, often turned off, but can be quickly restored and brought online. Data is available quickly and can be restored without much difficulty. However, a high level of competence and forward thinking is required to plan, build, and maintain it.
Option: A Hot Site
In this scenario, a duplicate computer center is available in a remote location from as little as a few miles to hundreds of miles away from the primary computer facility with communications lines set up and actively copying data at all times. At a minimum, the site has a duplicate of every critical server up and running with data that is up-to-date.
Option: The Cloud
By its very nature, the cloud is designed to handle business continuity; high availability; and disaster recovery. So that in the event of a disaster, management and staff can access business-critical applications and data anytime from anywhere. Cloud Services Providers (CSPs), like PCT, provide pooled resources, flexibility, scalability, security, and reliability to businesses of all sizes so that businesses can store their data, applications, systems, and services.
Don’t wait! Act!
Regardless of the option you choose, having a viable systems and data disaster recovery system is critical.
/Prime-Care-Technologies-Logo.png?width=191&height=55&name=Prime-Care-Technologies-Logo.png)


/PCT-Trans.png)