Downtime Threats
Cyber attacks, ransomware, and disasters threaten business-as-usual daily.
Cyber attacks, ransomware, and disasters threaten business-as-usual daily.
Scaling your IT cost-effectively as your business grows is critical to ongoing success.
Maintaining and optimizing your technologies is tough to keep up with.
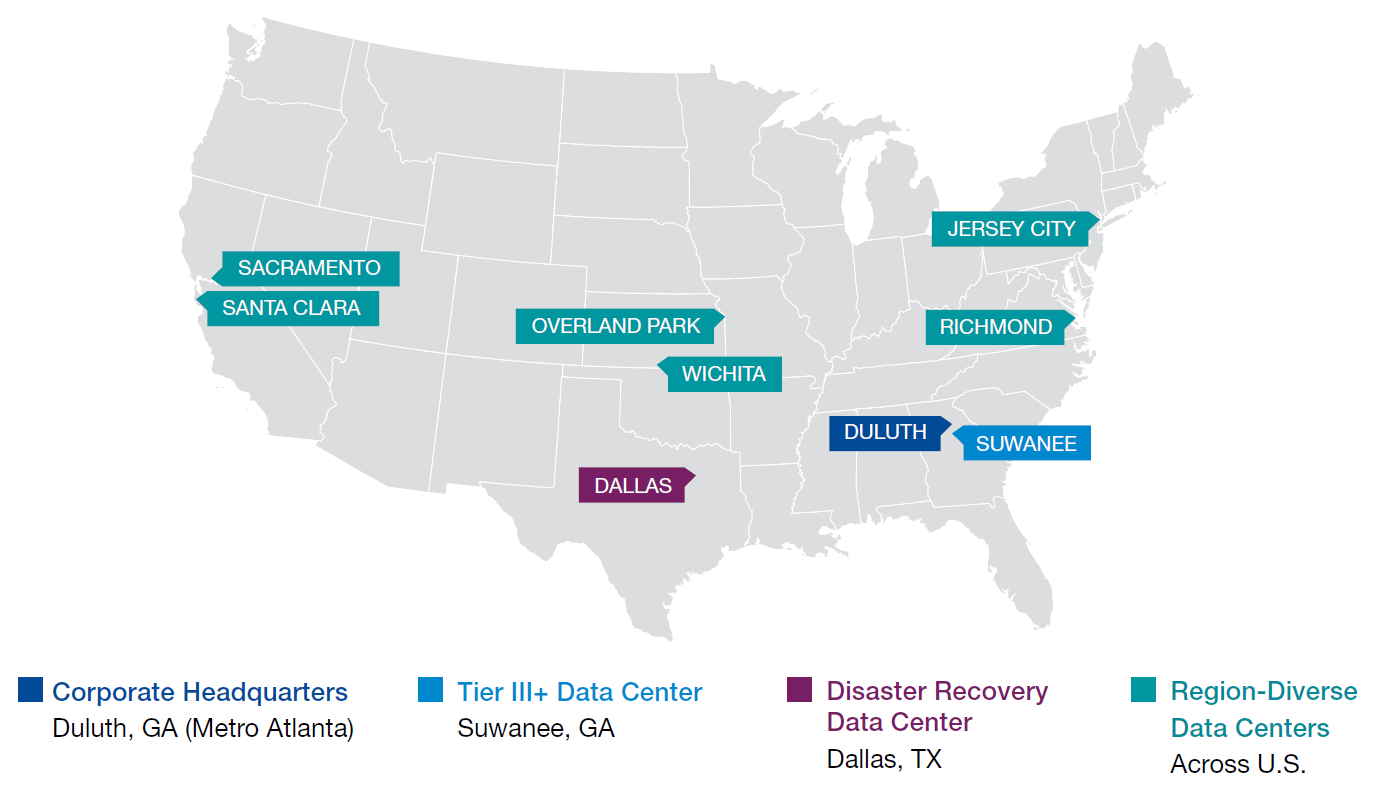
With privacy and security at the forefront of major industries, we understand how critical it is to protect your data and have reliable access to it.
/bait%26phish-1.png?width=435&height=116&name=bait%26phish-1.png)
/10zig.png?width=491&height=103&name=10zig.png)
/primeCLOUD-Partners/cisco_transparent.png?width=830&height=350&name=cisco_transparent.png)
/Partner-Kit/Citrix_transparent.png?width=210&height=69&name=Citrix_transparent.png)
/primeCLOUD-Partners/dell_transparent.png?width=150&height=150&name=dell_transparent.png)
/dell-emc.jpg?width=450&height=112&name=dell-emc.jpg)
/filecloud.jpg?width=459&height=111&name=filecloud.jpg)
/Partner-Kit/Fortinet_transparent.png?width=2560&height=310&name=Fortinet_transparent.png)
/Hipaa%20one%20logo.png?width=737&height=174&name=Hipaa%20one%20logo.png)
/Partner-Kit/ingram_transparent.png?width=2052&height=468&name=ingram_transparent.png)
/lenovo.png?width=281&height=92&name=lenovo.png)
/Partner-Kit/McAfee_transparent.png?width=2560&height=513&name=McAfee_transparent.png)
/Partner-Kit/Microsoft_transparent.png?width=2124&height=540&name=Microsoft_transparent.png)
/Mitel_logo-700x165.png?width=700&height=165&name=Mitel_logo-700x165.png)
/qts.jpg?width=300&height=156&name=qts.jpg)
/ruckus.jpg?width=499&height=167&name=ruckus.jpg)
/vmware.jpg?width=471&height=86&name=vmware.jpg)
Cyber Security attacks are on the rise. Employees today are exposed to sophisticated phishing, ransomware, and targeted C-level attacks. Without the right technology and training, your business is at risk. We also partner with IT vendors focused on key areas such as:

An important security layer to consider is called multi-factor authentication (MFA), also known as two-factor authentication (2FA). MFA protects us from hackers by ensuring that digital users are who they say they are. When MFA is enabled, a user must provide two or more pieces of evidence (or factors) to verify their identity and gain access to an app or digital resource.
There are three main types of MFA authentication methods:
MFA makes stealing your information much harder for the average criminal. The less enticing or harder to access your data it is, the more likely threat actors will choose someone else to target.
As the name implies, MFA blends at least two separate factors to verify it's actually you requesting access to your data. So even if a hacker has your user ID and password, MFA will require the entry of one more piece of information before granting access. It is a simple but powerful method to add a layer of extra protection so only authorized users access your data.
Various vendors offer MFA. A very common and effective MFA is to use an app loaded on your mobile phone or a key fob. Both receive a random number generated at regular intervals, usually 60 seconds, from the MFA vendor’s random number generator.
When entering your user ID and password to access an application or other digital resource, the last step is to enter the number displayed on the MFA app or key fob. Once you enter the correct number, the authentication process is complete and you have access.
We partner with best-of-kind MFA vendors if you need our help to get started.
More insurance carriers now require the implementation of MFA before issuing a cyber insurance policy. Depending on the carrier, they may require MFA for just Microsoft 365 Cloud Mail or Exchange OWA mail, or they may extend it to everyone’s login – as well as their devices.